If you have been following trends on mobile app security, you surely now understand just how important secure communication is for iOS apps. In December 2022 alone, there were approximately 2.2 million global mobile cyber-attacks, leaving mobile devices connected to the internet vulnerable to targeted threats and malicious activities. To avert cyber threats and data spying activities, an organization should buy an SSL certificate and install it on the website that can protect data in transit.
The threat of man-in-the-middle attacksamong others looms large, posing serious risks to sensitive data and user privacy.And that’s where SSL pinning comes in. It helps verify SSL/TLS certificates, to rebuff potential attacks and help you build trust with users.
How does SSL Pinning Work?
To begin with, the purpose of SSL pinning in iOS apps is to authenticate the legitimacy of SSL/TLS certificates. SSL pinning helps to avoid MiTM attack and saves data from being third party interception.
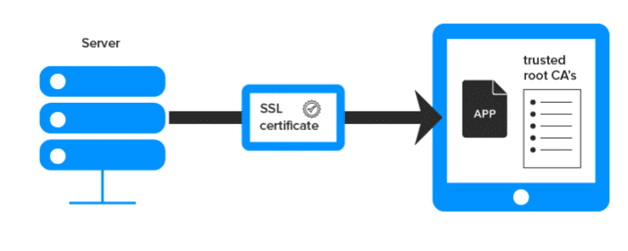
SSL certificate pinning operates on the principle of cryptographic security, employing a powerful mechanism to identify and verify the identity of servers or hosts.Rather than relying solely on certificate stores for verification, SSL pinning helps websites and platforms maintain a dedicated repository of trusted certificates.
Within this repository, secure and trustworthy SSL certificates are pinned, effectively blocking any attempts by suspicious servers to access the platform.To achieve this, users can create and store a list of approved SSL certificate issuers, which the application or website will utilize during communication setup.
This process serves as a double-check, reinforcing the usual mechanism that verifies connections.When a user attempts to establish a connection, SSL pinning comes into play as the second checkpoint.
The system cross-references the server certificate against the list of trusted issuers.If the connection is deemed trustworthy, it is established without issue.
However, if a malicious or fake certificate is detected, the user will receive a warning message or be denied access, protecting them from potential security threats. In essence, SSL pinning in iOS apps acts as a robust safeguard against unauthorized access and enhances the overall security of iOS applications.
How to Implement SSL pinning in iOS Apps?
We get it, if you’re trying to implement SSL pinning in your iOS app for the first time, it may sound a bit daunting. You shouldn’t fret though. For this guide, we will show you two easy methods for implementing SSL pinning in iOS apps;
1. Method 1; Using URL Session
- Step 1, Obtain the Certificate: The first step is to extract the .der certificate for backend application to which your mobile app should connect. You can also use a certificate in .cer format. Place the certificate you generated in the root of your project. Read how to generate a CSR on this page.
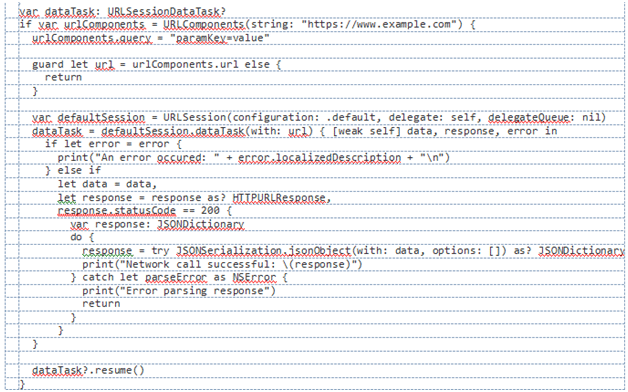
- Step 2, Add URLSessionDelegate: In your ViewController or any class where you want to handle URLSessionDelegate and its authentication challenge, declare a variable to load your certificate for comparison. Here’s an example with ViewController:

- Step 3, Perform Network Call:Now here, we willimplement a simple network call. We will use URLSession and pass MyViewController as the delegate:
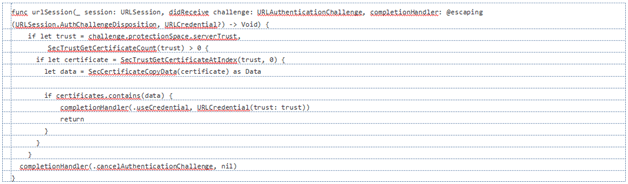
- Step 4, Implement SSL Pinning: Now comes the main part of SSL pinning in iOS apps, which involves the urlSession delegate method. It provides the serverTrust object representing your server’s SSL transaction state. To ensure a secure SSL handshake, perform the following checks:
- Check the certificate count in the trust object. It should be greater than zero
- Verify certificates in the certificate chain. One of them should match with the certificate pinned in the app.
2. Using Alamofire and ServerTrustPolicyManager
Alamofire, a widely used Swift-based networking library for iOS, provides a solid solution for SSL pinning through ServerTrustPolicy. This method evaluates the server trust, typically provided by an NSURLAuthenticationChallenge, when establishing a secure HTTPS connection to a backend server. Here’s how to implement SSL pinning in your iOS app using Alamofire and ServerTrustPolicy.
- Step 1, Basic Configuration for Alamofire Manager: To start, create a URLSessionConfiguration with default settings for Alamofire. This configuration will be used to set up the session manager.
Swift
- Step 2, Obtain and Load the Server’s Public Certificate: Retrieve your backend server’s public certificate in .der format (you can also use .cer format). Ensure your app targets this certificate for the connection. Place the .der certificate in your project, preferably in the “assets/certificate” directory.
Swift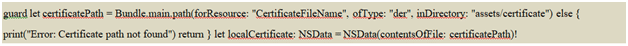
- Step 3, Set Up ServerTrustPolicy for SSL Pinning: Create a ServerTrustPolicy that uses the pinned certificate for validation. Set validateCertificateChain and validateHost to true to ensure a secure connection.
Swift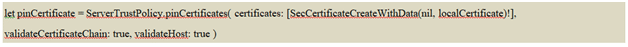
- Step 4, Associate the Certificate with the Server’s Domain: Map the server’s domain (e.g., “www.example.com”) to the previously created ServerTrustPolicy. If your app connects with multiple back ends, set up certificates for each backend system similarly.
Swift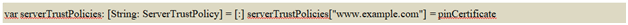
- Step 5, Create Alamofire Session Manager: Using the previously configured URLSessionConfiguration and the created serverTrustPolicies, set up an AlamofireSessionManager with SSL pinning.
Swift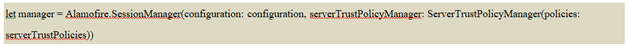
- Step 6, Connect with the Backend and Trigger the REST Service Call: With the manager in place, you can now initiate secure connections to the backend server.
Swift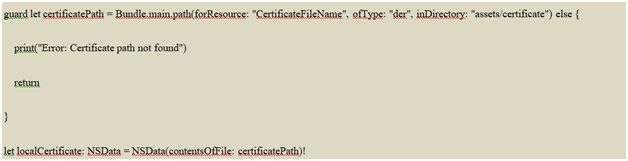
What is the Best Practice for SSL Pinning?
To ensure robust security in your iOS app, implementing SSL pinning is just the first step. Adherence to best practices is crucial to fortify your defenses against cyber threats. Here are some essential practices that will bolster your SSL pinning strategy and keep your app and user data safe from harm.
- Preventing Certificate Expiration Bypass: Keeping your SSL certificates up-to-date is vital to maintaining a secure connection between your app and the server. Regularly check for certificate expiration and promptly update them when needed. Failure to do so can create loopholes for attackers to exploit and compromise the integrity of your app’s communication.
- Guard against Reverse Engineering: Cybercriminals are always on the prowl for vulnerabilities to exploit. Implement code obfuscation techniques to deter attackers from reverse engineering your app’s code and gaining unauthorized access to sensitive information. Obfuscated code makes it significantly more challenging for attackers to decipher your app’s inner workings and safeguards your SSL pinning implementation.
- Regular Maintenance and Security Reviews: Security threats constantly evolve, and it’s crucial to stay ahead of potential risks. Schedule periodic security reviews to assess the effectiveness of your SSL pinning implementation and identify any weak points. Conduct regular updates to address emerging threats and ensure your app’s security remains at its peak.
In Closing
SSL pinning is key for fortifying the security of iOS apps. Developers must prioritize user data protection and build trust through reliable security practices like SSL pinning. This way, it will be easier to safeguard users’ data in the ever-changing security landscape.