New Prototype Gadget CIDS – Stops Vehicular Attacks
Car-harking demo seems to get all the credit in the security research community through remotely paralyzing Jeep on highway or cutting the brakes of a Corvette through its Internet-connected insurance dongle. However as the emerging automotive security field tends to progress, defensive tricks seems to be getting smarter too and now there seems to be a new prototype gadget which stops those vehicular attacks with an inventive hack of its own.
It has been mentioned in a paper that the researchers of University of Michigan, Kyong-Tak Cho and Kang Shine intend to present at the Usenix security conference next month, an easy-to-assemble tool which they call the Clock-based Intrusion Detection System, or CIDS. CIDS has been designed to spot the malicious messages car hackers tend to utilise in controlling the vehicle components such as brakes and transmission.
The CIDS model uses a latest technique in identifying attack messages and records the communications on the internal network of the car known as a CAN bus and within seconds tends to create fingerprints for each digital component of a vehicle which is called the Electronic Control Units of ECUs which enable everything from brakes to windshield wipers to communication.
CIDS-Fingerprinting – Tiny Timing Flaws – Clock Skew
In order to perform the fingerprinting, a strange characteristic of all computers is utilised, tiny timing flaws known as `clock skew’. Considering that those flaws may differ in every computer, inclusive of every computer within a car, the researchers could assign a fingerprint to each ECU depending on its precise clock skew.
The device of the CIDS then utilises those fingerprints to discern between the ECUs as well as to notice when one ECU imitates another such as when a hacker tends to corrupt the radio system of the vehicle to send-up messages which expected to be coming from a brake pedal or steering system.
This type of impression is significant to how white hat hackers earlier managed to mess with vehicles’ brakes, steering system and transmission, remotely.
None have used the clock skew to fingerprint car computer components before though the vital idea is not completely new. Security researchers had planned using clock skew identification on other computers for over a decade.
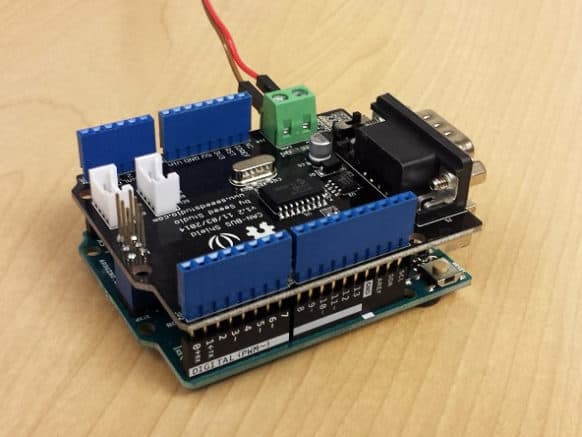
Model Built with Arduino Uno Board
The trick is that the oscillating crystals computers used in tracking time have some differences depending on the defects of manufacturing and temperature.
Over a period of time, it means that the clock of the computer could drift if it is not continuously reset against a more precise clock through the internet. Since the ECU clocks of the car have been designed to enable signals to be sent at definite frequencies instead of certain times in a day, their clocks seem to drift without being corrected.
Kang Shin, the professor of the University of Michigan who had created CIDS together with graduate researcher Kyong Tak had said that since each clock drifts, depending on the message arrival, he can tell whether it is sent by the legitimate ECU of the car or someone else.
He can fingerprint it based on timing as per that clock. The gadget of Michigan researchers is only a proof of concept and they do not intend to construct a consumer product and are not yet releasing their code.
On the contrary, they published a detailed paper on the technique. The model is said to be built with an Arduino Uno board, a Seeed Studio CAN-BUS shield and some wiring, hardware which tends to cost around $50.



![Best SaaS Backup Solutions [Expert Reviewed + Security Analysis]](https://www.prodigitalweb.com/wp-content/uploads/2026/05/Best-SaaS-Backup-Solutions-145x100.png)