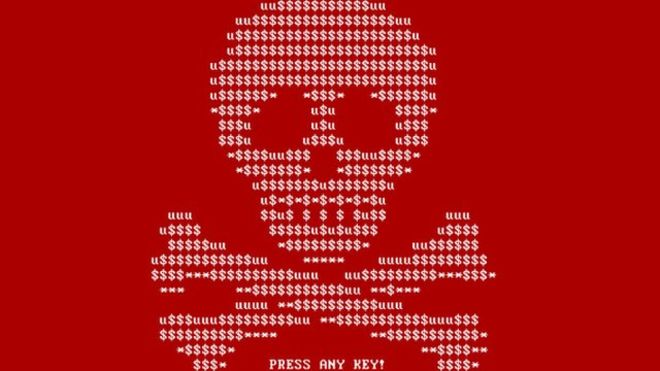
Petya Ransomware Victim can Unlock Infected Computers
Victims of Petya ransomware can now unlock their infected computers without making any payment to cybercriminals. An unnamed programmer has developed a tool which tends to exploit shortfalls like the malware encrypts a file that enables Windows to start up. In notes that are put on code sharing site Github, he had mentioned that key generator has been produced in order to help his father-in-law unlock his Petya-encrypted computer. Petya seemed to appear on the radar of the researchers last month when criminals distributed it to the companies through spam emails which posed as job applications.
It stood out from the other file encrypting ransomware program since it tends to overwrite a hard disk drive’s master boot record – MBR, thereby leaving infected computer incapable of booting in the operating system. The program tends to replace the legitimate MBR code of the drive that generally starts the operating system with code which encrypts the master file table – MFT showing a ransom note. The MFT is said to be a special file on NTFS volumes which comprise of information regarding all the other files, like the name, size and mapping to hard disk segments.
Key Generator Unlocks Petya-Encrypted Computer – Seven Seconds
The real contents of the files of the users are not encrypted though without the MFT, the OS does not know where these files are located on the disk. There is a possibility of utilising data recovery tools to reconstruct files though there is no guarantee that it could work perfectly and would be time-consuming. The malware that has begun circulating in huge numbers in March demanded a ransom of 0.9 bitcoins and hid itself in documents attached to emails claiming to come from individuals looking for work.
Lawrence Abrams, security researcher from the Bleeping Computer news site, stated that the key generator could unlock a Petya-encrypted computer in a matter of seven seconds. However the key generator needs the victims to extract some details from a particular memory location on the infected drive. Mr Abrams has mentioned that unfortunately for several victims, extracting this data does not seem to be an easy task and would probably involve removing the drive and then connecting it up to another virus free computer running on Windows.
Safety Secured Backups
Fabian Wosar from security firm Emsisoft has created a simple and free tool which can assist the victims. But since the infected computer cannot boot into Windows, using the tool needs taking out the affected hard drive and connecting it to a different computer where the tool could run. An external USB-based hard drive docking station could be utilised.
Data extracted by the tool should be entered into a Web application created by leostone which will utilise it to crack the key. Thereafter the user must put the affected hard drive back in the original computer, boot from it and enter the key on the ransom screen which is displayed by Petya.Graham Cluley, independent security analyst commented that there had been other incidents wherein ransomware makers had `bungled’ their encryption system.
Cryptolocker, Linux.coder and one other ransomware variant were all considered to be harmless when their scrambling schemes had been reverse-engineered. Mr Cluley had mentioned that the best thing was to have safety secured backups instead of relying on ransomware criminals goofing up.