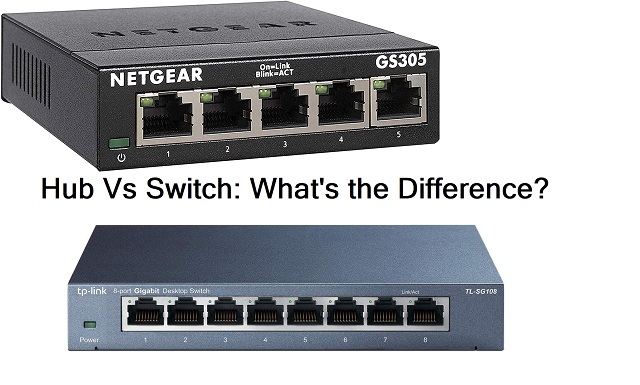
Let discuss and know the difference among the networking devices. Here is the comprehensive details of networking Hub Vs Switch.
What are Network Hubs:
A hub is employed in computer networking. It is an elementary networking device that helps you to connect multiple networking devices. In addition, it connects multiple networking devices together and making them act as a single network segment.
Besides, it does not have the routing tables and intelligence to send data packets and broadcast the network data signals across each and every network connection. They can detect basic network errors such as collisions. It broadcast all data to multiple ports connected it is a security risk, and sometimes it causes bottlenecks in data transmission. It works as a multiport repeater.
They are significantly cheaper. And they are the primary network devices that do not need an IP address. They are now obsolete and replaced by routers and switches now. An Ethernet hub has multiple input and output ports. The input ports’ data signal can appear at all output ports except the original incoming port. Some years back, connecting network segments by hubs is deprecated by IEEE 802.3 standard. It works at layer one of the OSI model (Physical layer).
What it can do?
Hub is designed to connect multiple networking devices or computers in a private network. It does not have any connection to internet access. When a hub receives data packets, it broadcast them to all other connected devices. Besides, it splits the network bandwidth between the connected devices. Therefore the fewer the connected networking devices, the more they have the bandwidth for each device. It means more connection speed to the shared device.
Hub works as a multiport repeater. It repeats the transmission received from one of its ports to all other ports. However, It can detect the Ethernet preamble (A 56 bits binary pattern, allowing the receiver to synchronize its clock to the transmitter), Interframe Spacing/Gap, collision by sending Jam Signal (Jam signal is a signal that carries a 32-bit binary pattern sent by the data transmission device.
In addition, It can handle only one transmission at a time. Besides, it has no memory to store the data. It runs on half-duplex (HDX) mode. Hubs are also named Concentrators because they function as a central connection point for a LAN.
Types of Hubs:
There are three types. They are
- Active or Multiport Repeaters
- Passive or Concentrators
- Intelligent Hubs
Passive Hubs:
The passive one does not amplify or regenerate the incoming data signals before re-broadcasting them in the network. They receive the data packet in one port and broadcast it to all other output ports. They do not improve the LAN performance and act passively. Usually, they employ Star Network configuration. It helps to identify the bugs and defective hardware in the network. Usually, they have a 10base-2port and RJ-45 connector to connect to the LAN.
Active Hubs:
They amplify incoming electrical pulses that contain data packers. They do not prioritize data packets. But they can be configured to examine the data pockets.
It can work as a firewall if configured. Besides, It can re-broadcast the weak signal by amplifying and applying retiming and resynchronization protocol.
In addition, it monitors the data packets sent to the connected networking computers. It plays a vital role in sending the data.
It uses store technology to check data before sending it out. In addition, It prioritizes the data packets first-come, first-serve basis. Besides, It can open the damaged pocket then direct and distribute the rest of the packets. If anything happens, they can resynchronize the data packets and transmit them again. Some time data packet cannot reach a designated port due to electromagnetic interruption in the cable. At that time, they can make up for the data loss.
Intelligent Hubs:
They provide all functions of Active one can do. Besides, It has remote management capabilities. In addition, it has an in-built microprocessor that helps to troubleshoot the network. They can allocate flexible data rates to the connected network devices. If any of the problems with a connected device can be easily detected, diagnosed, and resolved using the data management system of the Hub.
Features of Hub:
- Functions on the Physical Layer or the Layer one of the OSI Model
- It is a non-intelligent network device, and it will not filter data packets
- It primarily broadcasts the data signals. Therefore the collision domains of all nodes connected through the Hub stay one.
- Half-duplex is its transmission mode.
- Collision may occur inside the Hub.
- It is a passive device.
- Generally, they have lesser numbers of ports
- It works with shared bandwidth and broadcasting
- It includes only one collision domain and a broadcast domain.
- Hub does not support spanning tree protocol and cannot create a virtual local area network.
- Could not support networking like token ring
- No packet filtering
- They cannot provide routing capability
- Poor scalability
Application of Hub in Computer Networking:
- It used to create tiny home networks for connectivity
- It used to monitor the network
- Used for connectivity in Laboratories and Organizations
- It makes one device or peripherals such as a printer available throughout the network
Advantages of Hub:
The following are the Pros or the Advantages-
- Provide support for different network media
- It is economical
- Allows network Monitoring
- Backward compatible
- Extends the total distance of the network
- It will not impact the performance of the network
- It helps the nodes in the network to take part in the data transmission with the help of Protocol Analyzer.
Disadvantages of Hub
The following are the Disadvantages or the Cons-
- Half-Duplex means the data can be transmitted only one at a time. And therefore, it needs to change its mode alternatively and constantly. In other words, it cannot work on full-duplex mode and cannot be divided into segments
- Hub could not offer dedicated bandwidth to each connected device. Bandwidth needs to be shared among them, which will slow down the network when large Data is transmitted
- It could not decide or select the best bath of the network
- There is no mechanism to control or reduce network traffic
- It cannot support larger networks since the devices in the network share the data among all the devices.
- It does not have the mechanisms for collision detection
- Could not filter the data packets and information; therefore, it transmits packets to all the connected nodes
- It cannot function as the network architectures like the ring, token and more.
- Consumes unnecessary bandwidth
- It sends the data packets to unintended network connections, which may lead to a security threat
- Hubs are unable to differentiate between the connected devices on the connected network
What are Network Switches:
A network switch is hardware that connects the networking devices on a network using packet switching to send, receive and forward data packets or data frames to a destination node in the network. It works on the data link layer or layer 2 of the OSI model.
Like the Hub, Switch also has many ports. When data packets arrive at any of the network switches, it checks the destination addresses, performs a preliminary protocol check, and forwards it to the destination devices. It supports node to node unicast, multicast, and broadcast communication. Since the network switch learns the identities of the connected devices, it directly forwards the data to the network node.
Types of Switches:
They can be broadly differentiated into four types. They are;
- Unmanaged
- Managed
- Smart
- PoE
Unmanaged Switch:
It is less expensive. Typically it provides basic connectivity. Besides, It is commonly used in small offices and home networks. In addition, they are a plug-and-play model. It cannot be configured.
Similarly, it does have an interface or options to configure. Since you could not configure, you cannot assign an IP address. It relies on auto-negotiation between the network devices to establish communication between them. Besides, it automatically determines the best data transfer rate. In addition, it automatically shifts between full-duplex mode and half-duplex mode. If you prefer a switch that will do the basic functions of the network efficiently without customization, an unmanaged one is the best option for you.
Managed Switch:
This kind of device is costlier than the unmanaged ones. It has a console port. You can assign an IP address and configure it. Moreover, It bests suites to large and complex networks. It can be customized to augment the functionalities. The functionalities may be higher security level, network management, precision control, creating and modifying virtual LAN, etc.
Due to their scalability and flexibility, they are preferred mostly. Besides, it can be configuring with SNMP (simple network management protocol). You can control the entire traffic accessing your network. They are the best network switches that support the Gigabit standard of Ethernet. Most of the Managed devices are designed with Spanning Tree Protocol. It helps the administrators to perform quality control services. It is active and intelligent one.
Smart Switch:
They are intelligent with limited management features. They have a web interface with no CLI access that allows you to configure basic setups such as VLANs, port bandwidth, and duplex.
PoE Switch/ Injector:
PoE stands for Power over Ethernet. This PoE technology allows both Data and power transmission over the same cables. It means any connected devices such as a camera’s smart lighting system can function without any AC access or router. It offers greater flexibility and simplifies the cabling. With the help of Cat 5 cable, the PoE injector provides an additional power supply to the various connected devices to enable a home network.
Features of Network Switch:
- Functions in the Data Link Layer or Layer 2 of the OSI model.
- Since it is an active, intelligent network device, it can work as a multiport network bridge.
- It utilizes the MAC address to send data packets to the destination node. Maintain MAC address table
- It uses packet-switching technology to receive and forward data packets from the source to the destination node.
- Supports one-to-one, one-to-many, and one to all broadcast.
- It uses full-duplex mode transmission; therefore, communication in the channel occurs in both directions simultaneously. So collision will not occur.
- Equipped with network software and network management capabilities
- Can perform error checking before forwarding data to the destination port
- The numbers of ports are higher 24/48
- It works with fixed bandwidth
- It allows you to create virtual LAN
- Can control of who has access to various parts of the network
- It has provisions to monitor the network usage
Application of Switch:
- It helps to manage data flow across the entire network
- Local area network contains many numbers of linked managed switches
- It is generally used in the small office and home office environment
- It used in a computer network to connect multiple devices physically
- Can transfer data to any connected networking devices either using full-duplex mode or half-duplex mode.
Advantages of Switch:
The following are the Advantages or the Pros-
- It helps to connect multiple devices. It allows the star topology routing to connect multiple devices.
- As a bridge, it uses the same forwarding or filtering logic on each port to forward the message to a specific node. The Switch receives and decodes the frame header to read the Mac address of the message.
- It manages network traffic.
- It keeps the electrical signal pulses undistorted.
- Increase the LAN bandwidth by effectively handling the multiple collision domains with the broadband.
- It reduces the number of broadcast domains.
- Support VLANs to help in a logical segmentation of ports
- It makes use of the CAM table for the port to MAC mapping
- Reduces the workload on individual host
- Increase the overall performance of the network
- Minimize the frame collision with the help of collision domains created for each node
- It can be connected to the workstation directly.
Disadvantages of Switch:
The following are the Disadvantages or the Cons
- Minimize the number of broadcasts domains
- Not as good as a router to limiting the broadcasts
- Broadcast traffic is troublesome
- Communication between VLANs require VLAN routing
- It requires additional configuration and designing to handle multicast packets.
- It is quite challenging to trace connectivity issues
- Vulnerable to security attacks
- Switches minimize the casing impact on the network
- Minimize the frame collision
Hub Vs Switch Differences
The following are the Difference between Switch and Hub.
| Hub | Switch |
| Operate on Physical Layer | Operate on Data Link Layer |
| It performs Frame Flooding, which can be one to one, one to many, and one to all broadcast. | It performs broadcast and also performs one-to-one or one-to-many as and when needed. |
| Transmission Mode- Half Duplex | Transmission Mode-Full Duplex |
| It contains a single domain of collision | It contains several ports that include separate collision domains |
| Uses electrical signals or bits | Uses frames and data packets |
| Does not support Spanning Tree protocol | It supports Spanning Tree Protocol |
| Mostly collision occur in setup | Collision does not occur in Full-Duplex mode |
| Passive Device | Active Device |
| Not Capable of storing MAC addresses | Uses accessible content memory that application-specific integrated chips can access. |
| Not an intelligent device | Intelligent device |
| Network speed is up to 10 Mb per second | Speed varies from 10Mb per second to 10Gb per second |
| Do not use software | Uses software for administration |
| Packet filtering is not provided | Packet filtering is provided |
| It cannot be used as a repeater | It can be used as a repeater |
| Hacking of networking device is complex | Hacking of networking devices in the switch environment is easy |
| Have Maximum 4 ports | Can have 24 to 48 ports |
| Network gateway unable to recognize Mac address | Uses CAM table that ASIC generally accesses |
| It can not avoid switching loop | It can prevent switching loop |
Hub Vs Switch Security:
Since Hub is a passive, not intelligent device, it does not have any switching logic. But In the case of Switch, it has its own. But it needs to be appropriately configured; otherwise, an attacker can easily fool it out. A switch configured with exact routing information at the port level will strictly follow the routing information and only send the information to the exact port to protect the traffic. Switches have internal software and firmware for add-on security.