We use a few file compression software whenever we want to clear disk space. In this case, 7-Zip is a famous one that you can use. Multiple Windows users have used the program and found a new entry in the context menu, and we know the entry as CRC SHA.
Whenever you update to the program version 15.12 or install and call out the context menu, you may have seen the entry in this menu. While pointing the side arrow, you might get more entries, including CRC-64, SHA-256, SHA-1, etc.
What is CRC in Windows?
The term stands for Cyclic Redundancy Check. You can use the technique to identify errors in PC networks and correct them in digital data. Most recent communication is digital, i.e., sequence of 1’s and 0’s. You might see that a 0 exchanges 1 and a 1 replace 0.
It helps you to identify the errors in a sequence of bits. You can use the old process because you can embed the algorithm for Cyclic Redundancy Check into the hardware with some lines of code.
What is SHA?
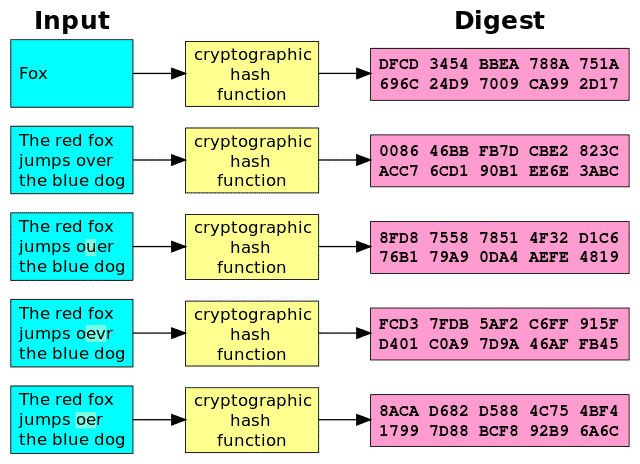
The term stands for Secure Hash Algorithm designed by the NSA and published by the National Institute of Standards and Technology. It is a family of cryptographic hash functions. You can use this to map variable length data into a message digest of a fixed length.
This case has various types, including 0, 1, 2, & 3. You can use the hash functions in information security applications, including digital signatures, message authentication codes, etc. Besides, it can check for the files you can download from the internet for any corruption.
What is CRC SHA?
CRC SHA stands for Cyclic Redundancy Check, Secure Hash Algorithm. It is a tool you can use to check the integrity of a file. For example, you should use it after downloading a file from the internet, which helps create a hash code for that file.
After that, your job is to compare the hash code from the developer with the hash that 7-Zip makes. If you find these similar, ensure that the downloaded file is not modified.
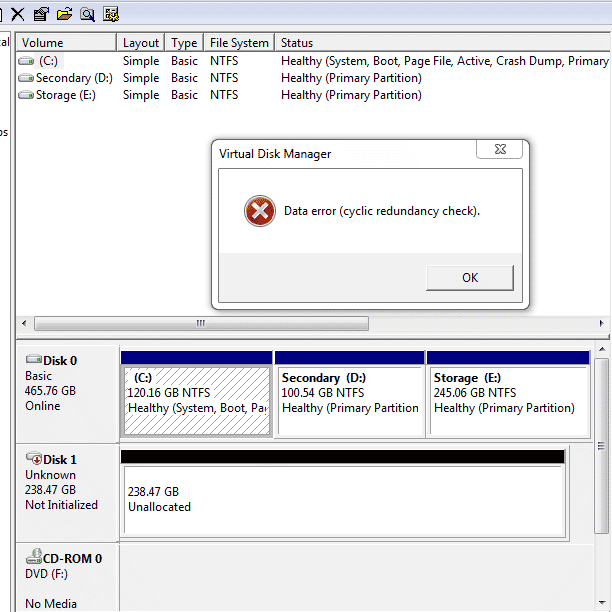
If you find the file contents modified, the hash code will change even if it is a minimal change. The file has been interfered with when you see that the hash code does not match. If you want to send confidential files, the tool is lucrative. Hence, you need to produce and add the hash code.
Is the Cyclic Redundancy Check, Secure Hash Algorithm tool Safe?
Multiple people installed 7-Zip but don’t know about the tool. They think of it as malware. Besides, some users wonder why it appears in the right-click menu of Windows.
We can assure you that the tool is safe to use. Therefore, you should keep the tool if you are thinking about the integrity of the files you downloaded from the internet. As a result, it is possible to create hash codes for the files.
Is it safe to remove the tool from your windows context menu?
You should confirm if it is safe whenever you plan to remove something from your PC. Is the file a system file that you want to remove? If yes, then you must think twice.
If you remove a system file, it can interfere with the working of your Windows OS. It can cause a system crash. However, you should know that the tool is not a system file. As it is not a preloaded file, you will not see any adverse effects on the workings of your computer. Therefore, whether you think that you don’t have to use the services that the tool offers, you may remove it. You don’t need to think about harming your PC.
How to remove CRC SHA from the Windows context menu:
Now, you get to know how the tool functions on the PC. So, let’s see how you can remove it. Whether you are willing to remove the entry from the right-click menu of the PC, go through the steps. You can perform the steps on any windows version.
- First, your task is to move to 7-Zip File Manager and open it. Hence, you should write 7-Zip in the Start search box. After that, hit the Enter key.
- When you go to the search results, your task is to tap on the 7-Zip File Manager to open the program.
- Next, you should choose Tools from the menu bar. Then, you have to tap on the Options menu item.
- Move to the Options page and then switch to the 7-Zip tab.
- You can see a checklist appearing. Then, you should find the CRC SHA option in the Context menu items. After that, you should uncheck it.
- Find the Apply button at the Window’s bottom. When you locate the button, you should tap on it to save the changes you have made.
You can get a message asking, “An event was unable to invoke any of the subscribers.” When you see the message, hit the OK button.
There is no need to restart the PC for the changes to take effect. As soon as you tap on any folder or file, you won’t see the CRC SHA option.
Whether you reach a point where you should re-enable the tool, go through the above steps to move to CRC SHA and check the checkbox. After that, you should tap on Apply to confirm and save the changes.
Removing the Tool:
If the entry in the context menu is lucrative, you can benefit from it but only while you know how to use it. However, you should remove the tool if you don’t want to use the tool more.
When you decide to remove the tool, ensure to evaluate the PC use. You may need the services provided by the tool in some operations. Perform the steps to remove the tool from Windows. You can go through the instructions carefully to remove it from the context menu.
Conclusion:
You should know that these two tools are used to identify an error in PC networking. Besides, these tools help you to check file integrity respectively. 7-Zip File Archiver application comes with the tool allowing you to check for the file authentication you downloaded from the internet.
Frequently Asked Questions:
- How can you add a context menu in Windows?
You can do it using the Registry method. It is a bit risky when people end up deleting something. In this case, you can use a context menu editor to add, remove, and edit Context Menu items in Windows. However, you can use other apps to perform safely. Ensure that you should back up the registry.
- How can you see the Secure Hash Algorithm value of any windows file?
You can see the value of any file using PowerShell. Suppose you want to see the value of the DLL file named secur32.dll below the system32 folder.
You can see PowerShell in the start menu. Enter the command given underneath:
get-filehash filelocation -Algorithm sha1
If the file location is C:\Windows\System32\secur32.dll
the command will be—
get-filehash C:\Windows\System32\secur32.dll -Algorithm sha1
- Why is the tool important?
The two tools are available as a single option in multiple software. You can use the tools to check the file’s integrity after downloading it from the internet. Hence, you need to offer a hash code to download it from the internet.
Your device will check both the new hash code and its hash code. If these are the same, unauthorized users can not modify or alter the downloaded file.




![Best SaaS Backup Solutions [Expert Reviewed + Security Analysis]](https://www.prodigitalweb.com/wp-content/uploads/2026/05/Best-SaaS-Backup-Solutions-145x100.png)