SSH, which stands for Secure Shell Protocol, refers to a cryptographic network protocol used to operate network services over an unsecured network securely. Remote login & command-line execution are the two most remarkable applications of it. Depending on a client–server architecture, these protocols connect an SSH client instance with an SSH server.
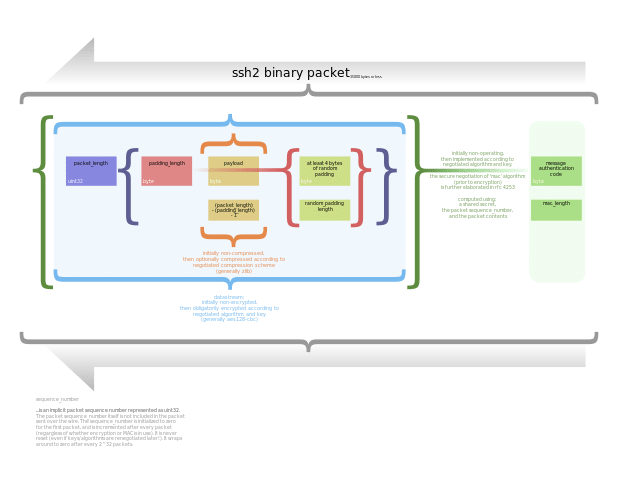
It is a layered protocol suite that comprises three principal hierarchical components: the transport layer, user authentication protocol, and connection protocol. While the first one offers server authentication, confidentiality, and integrity; the second one can validate the user to the server. The third one multiplexes the encrypted tunnel into many logical communication channels.
It was designed on OSs like Unix to work as a replacement for Telnet, unsecured remote Unix shell protocols like Berkeley Remote Shell (rsh), etc. It can be a replacement for related login and rexec protocols which use insecure transmission of authentication tokens.
What is SSH (Secure Shell) Protocol?
SSH is called Secure Shell or Secure Socket Shell. This one is a network protocol using which users, like system administrators, can access computers over an unsecured network. It indicates the suite of utilities implementing the SSH protocol. This protocol can offer strong password authentication and public key authentication. In addition, it provides encrypted data communications between two PCs connecting over an open network.
Along with offering strong encryption, network administrators use it widely to manage systems and applications remotely. Thus, it becomes easier to log in to another computer over a network, execute commands and transfer files from one computer to another.
With the help of a client-server model, the protocol connects an SSH client application with an ssh server. Hence, the SSH client indicates the end where the session is displayed. On the other hand, the SSH server indicates the end where the session runs. Supporting application protocols which are used for terminal emulation or file transfers often remain included in SSH implementation.
You can use SSH to make secure tunnels for other application protocols like running X Window System graphical sessions remotely in a secure way. The Ssh server listens on standard TCP port 22 by default.
How does SSH Protocol work?
There are insecure terminal emulation or login programs like Telnet, rlogin & rsh, and the shell was designed to exchange them. It allows you to log into and run terminal sessions on remote systems. Besides, this protocol can exchange file transfer programs like FTP or File Transfer Protocol and rcp or remote copy.
Basically, SSH is used to connect a remote host for a terminal session. Here is the form of the command:
Using the command, the client connects to the server called server.example.com with the user ID UserName. If you negotiate a connection between the local host and the server for the first time, you will be prompted with the remote host’s public key fingerprint. Then, it asks you to connect though there does not exist any prior connection.
Host’s authenticity ‘sample.ssh.com’ will not be established.
The fingerprint of DSA KEY is 01:23:45:67:89:ab:cd:ef:ff:fe:dc:ba:98:76:54:32:10.
Do you want to continue connecting (yes/no)?
If you answer yes, the prompt will continue the session. Then, you can see the host key is stored in the local system’s known_hosts file. In this regard, you should know that it is actually a hidden file that is stored by default in a hidden directory named /.ssh/known_hosts in the user’s home directory. When you store the host key in the known_hosts file, connecting directly to that server for the client system is possible without any approvals.
You should know that the secure connection of the protocol works differently on different OSs:
On Mac and Linux – via Terminal
On Windows – via an installed SSH client
Let’s dig into the article to know how SSH servers and SSH clients work.
What is an SSH Server?
It helps to initiate the network connection. In this case, you should know that the server is vigilant for new connections and gives responses to these with the help of the host system’s TCP port 22.
Whenever an SSH connection starts, the server should use public-key cryptography to authenticate itself to the client. It is important for the client to ensure that it is communicating with a legitimate server, not with an attacker. As soon as the server & client set up a safe connection, you can perform the following things:
- File transfers
- Remote command execution
- Remote host administration
- Other application traffic security
Hackers often target this server because it can offer remote access to the host system. So, the software quality needs to be high, while the server should have strict security requirements. It means that its code must prevent bugs and imperfections that may lead to unnecessary exposure.
What is SSH Client?
Once the system administrators install a program on local machines & remote PCs, they can get the advantage of secure connections. We call the software the Secure Socket Client. Several SSH client services are available on the web to select for local and remote PCs.
Mac and Linux devices mainly use a Terminal program to run ssh commands, whereas Windows OS needs a dedicated client program like PuTTY, KiTTY, MobaXterm, or WinSCP.
As soon as you install a client on a local machine, it is necessary to install an SSH server to accept shell connections. Thus, it is possible to start using the secure alternative to remote access options. Hence, the client works in a secure environment through which it is possible to connect to a remote host device.
For its authentication, you need to use your username and password. However, users can use a public-private key pair without a password to secure remote access management. We can say that the Shell keys play a crucial role in the SSH protocol.
What is SSH Used for?
People use these connections to secure various communications between a local machine and a remote host like— secure remote access to resources, remote execution of commands, delivery of software patches, updates & other administrative applications.
You can use SSH to create a secure channel between local and remote computers. Besides, it lets you manage routers, server hardware, virtualization platforms, operating systems (OSes), inside systems management, and file transfer applications.
People use Secure Shell with tools for connecting to servers, making changes, performing uploads, and exit. In addition, it is possible to do this through the terminal directly. You can employ SSH keys to automate access to servers. These are useful in scripts, backup systems, and configuration management tools.
The shell keys offer single sign-on (SSO), making them easy to use. Therefore, these can work across organizational boundaries. You don’t need to type a password (every time) whenever you want to move between your accounts.
If it comes to talk about playing central roles in identity management and access management, SSH performs more than authenticate over the encrypted connection. You can find all traffic of the protocol encrypted. It means that all your activities remain private, like browsing the web, sharing files, or running a command.
You can use the protocol with a normal user ID and password as credentials. Sometimes, the shell depends on public key pairs that can authenticate hosts to each other. If you want to connect to the remote host, you should employ your user ID and password, or you can try other authentication processes. However, for authenticating separately to each other, remote machines and local machines can create a unique public key pair for every host in communication. In this regard, you should know that a single session needs two public key pairs where one pair helps in the authentication of the remote machine with the local machine. On the other hand, the second pair helps to authenticate the local machine to the remote machine.
How to Install SSH Secure Shell:
- Your first task is to open a web browser program like Netscape Communicator or Internet Explorer.
- When you enter the Location field, you should type this URL:
http://exampledotcom/Win/Docs/ssh.html
-
-
- Then, you will get to see a screen like the following.
- Then, you should hit ENTER.
- After that, tap on the Install SSH Secure Shell link.
- After that, the Save As dialog box will appear.
- Once you enter the Save As dialog box, your task is to hit the Desktop icon in the left column of the dialog box.
- Then, your task is to tap on Save.
- After that, your job is to close browser programs and other open programs.
- You need to find the file’s location called, SSHSecureShellClient-3.2.0, on your PC. The full name may not appear until you hit the icon.
- You should tap twice the icon to execute the installer program, which extracts the necessary files to install the program.
- Then, the SSH Secure Shell for Workstations 3.2 Setup dialog box appears.
- Now, you should tap on Next.
- After that, you must accept the license agreement by tapping Yes.
- Then, the Choose Destination Location dialog box will appear in front of you.
- After that, you need to tap on Next.
- Now, the Select Program Folder dialog box will appear.
- Then, you need to tap on Next.
- Now, the Select Components dialog box will appear.
- Ensure that the checkbox on the display’s left side contains a check mark.
- Then, your task is to tap on Next.
- Now, the Check Setup Information dialog box will appear.
- Tap on Next. You can see the program installed automatically. The progress of the installation method can be seen on the progress bar.
- Once you install the program successfully, you can see the Setup Complete dialog box.
- Finally, tap on Finish.
-
How to Delete the Installation File:
-
-
- If you install the program, the installation (.exe) file is not necessary. Therefore, you can delete it. Following the instructions, you need to delete only the file that is used to install SSH Secure Shell, don’t delete the program.
- Then, you need to right-click on the SSHSecureShellClient-3.2.0 icon.
- When you will get to see the drop-down menu, you have to choose the option: Delete.
- Finally, your task is to tap on Yes to delete the file.
-
How to Set Up a Connection to Sheaf:
Your first task is to tap the SSH Secure Shell File Transfer Client desktop icon twice.
-
-
- You should perform the steps only when you connect to sheaf every working session for the first time.
- The SSH Secure File Transfer dialog box will appear thereafter.
- Then, you need to hit the folder icon on the left side of the Profiles Menu.
- A dialog box will appear.
- Now, you should choose Add Profile.
- Then, a dialog box will appear.
- You should now type sheaf in the Add Profile dialog box.
- After that, you have to tap on Add to Profiles.
- You should hit the folder icon on the Profiles Menu’s left side.
- Now, you should choose Edit Profiles.
- Now, you need to choose the sheaf under the profiles folder which can be seen on the screen’s left side.
- Then, the Profiles dialog box will appear.
- The display’s right side contains fields to set up a connection to the sheaf.
- Next, your job is to type sheaf.nss.udel.edu in the Hostname field.
- After that, you have to hit the TAB key.
- When you enter the User name field, you should type the UNIX username indicating a portion of the email address before @udel.edu.
- You should choose xterm to use the drop-down arrow to the Terminal answerback field’s right side.
- Now, you need to tap on OK.
- Tap on the default ftp profile, which is on the Profiles dialog box’s left side.
- You should type the path in the Hostname field to the folder where you are willing to share files. For instance, /opt/home/psoft/clientSw/hr/io/usert1/department directory.
- You need to insert the correct department directory from the following list:
-
Ag–ag
Bookstore–bk
Development–devel
Library–library
Review–review
Student Center–sctr
User Services–us
-
-
- Finally, you should tap on OK.
-
How to Transfer Files to Sheaf using the SSH Secure File Transfer Client?
Before using the program properly, making two new folders on the PC–c:\time and c:\My Documents\timesheets is essential. Have you not done this yet? Then, you should follow the instructions.
-
-
- Your first task is to open the SSH Secure Shell File Transfer Client. If you have opened the program already, you can skip it.
- If you want to log on to sheaf, you should tap on the Profiles Menu.
- After that, you have to choose the option sheaf.
- Are you logging in for the first time? Then, you will view the Host Identification dialog box. After that, you must tap on Yes.
- Now, you must type the password in the Enter Password dialog box.
- Next, you have to tap on OK.
- Tap on the white upward pointing arrow on the toolbar for uploading files.
- Then, a dialog box will appear.
- You need to tap twice on the time folder. People who have still not made a c:\time and a c:\My Documents\timesheets folder must follow the instructions before doing anything.
- Tap twice on the c:\time folder.
- Now, your task is to choose the file(s) you are willing to share (.dat files). Hence, it is possible to choose multiple files. You only have to hold down the CONTROL key and tap on the name of every file.
- Next, you should tap on Upload.
- After that, your job is to choose the option Disconnect by navigating to the File Menu to shut down the connection to sheaf.
- Then, the Confirm Disconnect dialog box appears.
- Next, your task is to tap on OK.
- Choose Exit from the File Menu to exit the program.
- A dialog box will appear thereafter.
- At last, you can see the program is closed.
-
Secure Shell capabilities:
These are the functions of the secure shell.
-
-
- secure remote access to SSH-enabled network systems or devices for users and automated processes;
- secure and interactive file transfer sessions;
- automated and secure file transfers;
- secure issuance of commands on remote devices or systems; and
- secure management of network infrastructure components.
-
You can use the shell interactively to enable terminal sessions. Besides, people can use it instead of using the less secure Telnet program. You can use this protocol in scripts and other software so that programs & systems can access data securely & remotely.
The History of SSH:
Tatu Ylönen, a researcher at the Helsinki University of Technology, designed the first-ever version of SSH. The first version of it appeared in 1995. Later, he began SSH Communications Security, a Finland cybersecurity vendor.
Several flaws were discovered in SSH-1 over time. But the version is now considered unsafe to use.
SSH-2 is the current version adopted as a Standards Track specification by IETF or the Internet Engineering Task Force in 2006. Remember that it doesn’t support SSH-1. It uses a Diffie-Hellman key exchange and a more powerful integrity check which can enhance the security level by using message authentication codes.
SSH clients and servers use several encryption methods used, broadly being Advanced Encryption Standard (AES) and Blowfish. Although SSH-2 doesn’t have exploitable vulnerabilities, as per the leaked information of Edward Snowden in 2013, NSA or National Security Agency can decrypt a few SSH traffic.
Secure Shell Security Problems:
Enterprises that use the shell need to consider finding ways so that you can manage the host keys which remain stored on client systems. The keys accumulate over time for IT staff that must have the capability of accessing remote hosts for management purposes.
Data stored in the SSH known_hosts files could be used to gain authenticated access to remote systems. That is why organizations must be conscious of the existence of the files. These must have a standard procedure to retain control over the files even despite a system being taken out of commission because hard drives can keep the data stored in plaintext.
As a developer, you must be careful when you incorporate SSH commands or functions in a script or other programs. You can issue an SSH command with a user ID and password for authentication of the user of the local machine to an account on the remote host. But remember that credentials can be exposed to attackers with access to the source code.
Shellshock refers to a security hole in the Bash command processor, which you can execute over SSH. But remember that there is no vulnerability in ssh, but it is in Bash. Poor key management is the major drawback of SSH.
SSH vs. Telnet:
Telnet was an internet application protocol used to initiate a terminal emulation session. Besides, it can maintain this emulation session on a remote host.
Based on the functionality, both are similar. So what makes these different is that the secure shell protocol authenticates endpoints using public key cryptography while setting up a terminal session and encrypting session commands and output.
People use telnet for terminal emulation, whereas the secure shell does terminal emulation. You can use this to issue commands remotely, as with rsh, transfer files using SFTP or SSH File Transfer Protocol, and tunnel other applications.
SSH vs. SSL/TLS:
TLS, which stands for Transport Layer Security protocol, can update the Secure Sockets Layer (SSL) protocol. It was specially designed to offer security for network transmissions at the transport layer. Above or at the transport layer, the Secure shell protocol operates. However, some major differences are there between these two.
Both indeed depend on public/private key pairs to authenticate hosts. But the server is only authenticated with a key pair under TLS. If it comes to talk about secure shell protocol, it uses a separate key pair for the authentication of every connection. One key pair is for a connection from a local machine to a remote machine, while the other one is to authenticate the connection.
There is another difference between SSH and TLS. TLS either encrypts connections without authentication or authenticates connections without encryption. But the secure shell can do both to all connections.
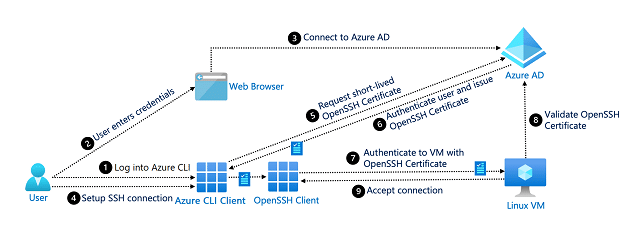
The shell protocol can offer a secure mechanism for IT and information security (infosec) professionals to remotely manage SSH clients. Hence, you don’t need password authentication for starting a connection between the server and an SSH client. Ssh is capable of authenticating the devices themselves. Therefore, IT staff can connect with remote systems and modify the Secure shell configurations, like adding host key pair or removing it in the known_hosts file.
SSH Implementations:
This open protocol has been implemented for most computing platforms. Depending on BSD or Berkeley Software Distribution, the open source OpenSSH implementation can be discovered on Linux, Unix, and other OSes.
In 2015, OpenSSH began running in Windows PowerShell. Later in 2018, optional OpenSSH support was added to Windows 10. In Unix-like OSes, people can access SSH directly by default. However, enabling Microsoft’s ported version of OpenSSH in the Windows Settings application is essential.
PuTTY is an instance of a secure shell’s open-source implementation. Although PuTTY is currently available for Windows, macOS, and Unix/BSD, it was written mainly for running on Windows. Since a prolonged period, it is considered as the top option to use the protocol on Windows OS.
Ssh suite’s most implementations comprise three utilities, including-
slogin (secure login)
ssh
scp (secure copy)
The secure versions of these insecure Unix utilities are rlogin, rsh, and rcp. SSH can authenticate remote PCs by using public key cryptography. Besides, it helps to enable the remote PC to authenticate the user. However, you can see a lot of SSH implementations for different platforms and under different open-source and proprietary licenses.
What is the SSH Command?
You have already come to learn that there are several graphical implementations of SSH. However, this program mainly gets invoked at the command line or executed as a script’s part. If you run the ssh command yourself without any arguments like a destination host or user ID, it will return a list of SSH command parameters & options.
The basic command form invokes the program and destination host name or IP address.
ssh server.example.org
It connects to the destination, server.example.org.
The destination host prompts for a password to give a response for the account user ID under which the client is running. Suppose the user ID is jsmith. Then, you will be asked by the remote host for a password connected with the account jsmith.
The user ID is different for the remote host. Therefore, the command is necessary to be issued with the remote host user ID in this way:-
Using ssh from the command line is possible if you want to issue a single command on the remote host. Then, you should exit. For instance,
ssh example.org ls.
It executes the Unix ls command listing all current directory’s contents on the remote host.
You should know that it is the sshd that initiates the SSH server. This server waits until the incoming requests are received. Then it enables the authorized system for connecting the local host. Whereas ssh-keygen is a program. It is used for creating a new authentication key pair for SSH that users can use to implement SSO. Moreover, it can be used to automate logins and authenticate hosts. Whereas you can ssh-copy-id for installing, copying and configuring SSH keys on the server for automating logins without passwords.
What is SSH Tunnelling?
It is called SSH port forwarding. With the help of this technique, you can open a secure tunnel between a local host and a remote host. It can redirect network traffic to a specific port/IP address so that applications can access a remote host directly on the local host. You can find the destination on the remote SSH server which could be configured to forward to another remote host.
The tunnels are powerful tools for IT administrators, and malicious actors as they are capable of transiting an enterprise firewall undetected. So, you can get tools preventing the unauthorized use of these tunnels via a corporate firewall.
Is SSH vulnerable?
Remember that secure shell communications security is not perfect. These flaws mainly stem from SSH keys and their improper use. For instance, hackers can steal SSH keys and use these thereafter as a backdoor to vulnerable systems. It is generally connected to people who especially focus on protecting their credentials only and forget completely about the keys’ security.
The issue is if hackers can access SSH keys, they can also access other keys stored on the device. When they get their hands on some keys, they can get remote user access to the whole company.
Let’s see some SSH vulnerabilities about which you must be cautious:-
-
-
- Inadequate SSH key tracking
- Frequent sharing of SSH keys
- Static SSH keys and embedded keys
-
Inadequate SSH key tracking:
Big companies accumulate a lot of SSH keys. If these have ten thousand or more servers, they will have millions of keys. So, it can happen that they lose track of a few of them. As a result, hackers get the chance to get access to unaccounted keys. It helps them to gain long-term access to the company.
Frequent sharing of SSH keys:
A few employees duplicate keys because according to them, they can use these more efficiently. You should know that hackers require only some keys to gain unauthorized access. It is why SSH key sharing must be monitored closely and limited when possible.
Static SSH keys and embedded keys:
Security professionals and IT administrators do not change the keys often as they think that something might be forgotten along the way. It may generate plenty of static keys to open a backdoor for potential hackers. In addition, keys embedded within scripts and applications may be static. You can find administrators avoiding making any changes because of not understanding the underlying code, and they are not interested in causing a system outage. However, remember that these specific keys may be problematic, like other static SSH keys.
Conclusion:
The Secure Shell protocol can be one of the most complicated network protocols. There is a simple reason for its fame and wide usage which is communication between the SSH client and server is encrypted completely.
However, the SSH protocol has a few flaws. However, this protocol is still far better than other authentication methods. This protocol is effective for businesses which can transfer files and communicate over the network securely. This article will be helpful for those who are planning to start using the protocol.
Frequently Asked Questions:
-
-
- What does SSH stand for?
-
It stands for “Secure Shell.”
-
-
- What does SSH do in Linux?
-
Secure Shell Protocol can offer a secure encrypted connection between two hosts over an insecure network.
-
-
- Is PuTTY an SSH?
-
It is actually a versatile terminal program for Windows. It is considered as the world’s most famous free SSH client.



![Best SaaS Backup Solutions [Expert Reviewed + Security Analysis]](https://www.prodigitalweb.com/wp-content/uploads/2026/05/Best-SaaS-Backup-Solutions-145x100.png)